In the intricate world of cybersecurity, the narrative often centers on sophisticated firewalls, impenetrable encryption, and cutting-edge threat detection systems. Yet, beneath this technological veneer lies a stark, often overlooked truth: the most formidable challenge isn’t the technology itself, but the human element. Every major breach that makes headlines, from data leaks to system outages, frequently originates not from a brute-force attack on a server farm, but from a seemingly innocuous action by a single employee – a click, an email, an unwitting download. This “Patient Zero” moment is the critical vulnerability, a tiny crack through which an entire digital empire can crumble.
The Human Element in Cyber Warfare
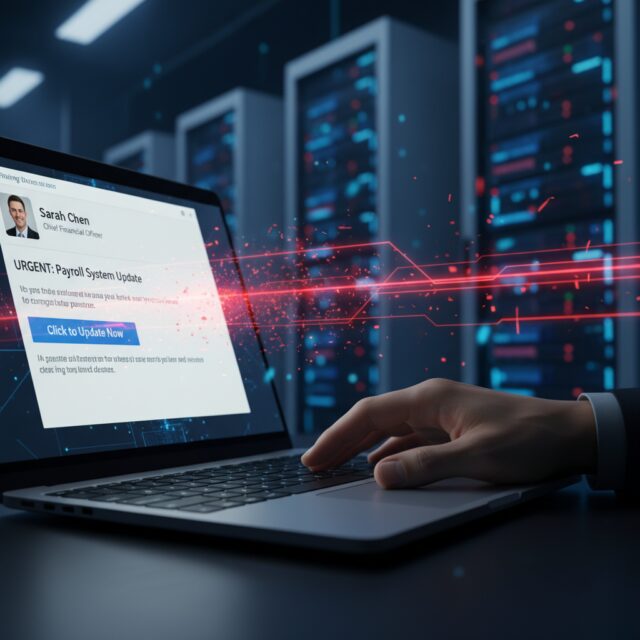
Despite billions invested in security infrastructure, the human factor remains the weakest link in the cyber defense chain. Phishing emails, social engineering tactics, and carefully crafted malware campaigns are designed to exploit trust, curiosity, or urgency. These aren’t random attacks; they are precision strikes aimed at individuals, turning unwitting employees into the initial vectors for compromise. It’s a testament to the ingenuity of attackers that they consistently find ways to bypass technical safeguards by simply targeting the person behind the keyboard.
Understanding this fundamental vulnerability is the first step towards building a truly resilient security posture. It’s not about blaming employees, but acknowledging that even the most security-aware individual can fall victim to a highly sophisticated and personalized attack. The pressure to perform, the speed of modern business, and the sheer volume of digital interactions create an environment ripe for exploitation, where a moment of distraction can have catastrophic consequences.
The Evolving Threat: AI-Powered “First Clicks”
Looking ahead to 2026, the landscape of initial compromise is becoming exponentially more perilous. Threat actors are no longer relying solely on generic phishing templates. Instead, they are leveraging Artificial Intelligence to craft hyper-realistic, contextually relevant, and almost impossible-to-spot “first click” attacks. AI can analyze vast amounts of public data to create highly personalized emails, deepfake voices for convincing vishing calls, and even mimic legitimate internal communications with startling accuracy. This level of sophistication means that the traditional markers of a malicious email – grammatical errors, suspicious links, unusual sender addresses – are rapidly disappearing.
Imagine an email from a seemingly familiar colleague, discussing a project you’re actively working on, complete with internal jargon and a perfectly legitimate-looking attachment. An AI could generate this in moments, tailoring it specifically to your role and recent activities. The line between legitimate and malicious content blurs to the point of invisibility, making it incredibly difficult for even trained professionals to discern the threat without advanced tools and an unwavering vigilance.
“Patient Zero”: The Inevitable First Infection
Given the escalating sophistication of AI-driven attacks and the inherent fallibility of humans, the concept of a “Patient Zero” infection is no longer a theoretical risk but an almost inevitable precursor to a larger incident. It’s not a question of if a single laptop or workstation will be compromised, but when. The critical challenge then shifts from absolute prevention – a goal that is increasingly elusive – to rapid detection and, more importantly, immediate containment. Once “Patient Zero” is infected, the clock starts ticking.
The danger lies in the speed with which these initial breaches can escalate. Modern malware often possesses lateral movement capabilities, designed to spread rapidly across networks, elevate privileges, and establish persistence before detection. A single compromised endpoint can become a beachhead for an entire network takeover, exfiltrating sensitive data, deploying ransomware, or disrupting critical operations within minutes or hours.
Beyond Detection: The Need for Rapid Containment
Traditional cybersecurity strategies have heavily emphasized perimeter defense and anomaly detection. While vital, these are often insufficient against stealth breaches initiated by a “Patient Zero.” The focus must expand to include robust, pre-planned rapid containment protocols. This isn’t just about identifying the threat; it’s about having the capability to isolate it, neutralize it, and prevent its spread with extreme prejudice and speed. The ability to execute a “total shutdown” of a compromised segment or asset at a moment’s notice becomes paramount.
Such a strategy requires more than just technology; it demands a well-drilled incident response plan, clear lines of authority, and automated tools capable of swift action. Can your security team, at 3 AM, identify a compromised workstation and automatically disconnect it from the network, revoke its credentials, and quarantine its data before the threat can propagate? This level of preparedness is the difference between a minor incident and a catastrophic breach.
Crafting Your Total Shutdown Strategy
Developing a “total shutdown” strategy involves several critical components. Firstly, it requires a deep understanding of your network architecture and the ability to segment it effectively, creating firebreaks that can limit lateral movement. Secondly, it necessitates advanced endpoint detection and response (EDR) solutions that can not only identify malicious activity but also initiate automated response actions. Thirdly, a comprehensive incident response plan, regularly tested through simulations and tabletop exercises, is indispensable. This plan must define roles, communication protocols, and specific actions for various types of “Patient Zero” scenarios.
Finally, continuous employee training, focusing on recognizing evolving AI-powered threats and understanding the critical role they play in the overall security posture, remains crucial. While prevention may not be absolute, empowering employees to be the first line of defense, coupled with a robust, rapid containment strategy, transforms them from potential vulnerabilities into active participants in the fight against cyber threats. The future of cybersecurity success hinges not just on preventing the first click, but on having an ironclad plan to contain its fallout instantly, ensuring that a single point of failure doesn’t lead to a total collapse.